Mobile device forensics & digital investigationMonthly report n⁰12- 2023-01https://pts-project.org/blog/monthly-report-n12-2023-01/Context of the projectPiRogue Tool Suite is a reboot of PiRanhaLysis project. Today, PiRanhaLysis is used by a lot of people ranging from universities (the University of Yale as an example), activists, NGOs and gets a lot of traction. Too much traction in fact to be maintained in our spare time as we have done until now. Currently, the project is at the proof-of-concept stage. To get to wider adoption by the general public, we need to streamline the build process and smooth the interface. Our goal is to make the project accessible to anyone. The projectThe problem: the lack of open-source means (hardware + software) to assess both privacy and security of mobile devices. Depending on HRD goals, they should want to educate, conduct emergency assessment or off-the-field investigations. The plan: As with all the other projects we do, we are the first users of the technologies we develop and we aim to provide open-source, low-cost, well maintained, easy to use and easy to build hardware and software. We have three functioning modes for PTS:
The PiRogue is an open hardware device based on a Raspberry Pi operating as a network router (like any ISP router) analyzing network traffic in real time. What we have done so farYou can check out our work on GitHub at https://github.com/PiRogueToolSuite/ or on our website at https://pts-project.org/. PiRogueWe have published:
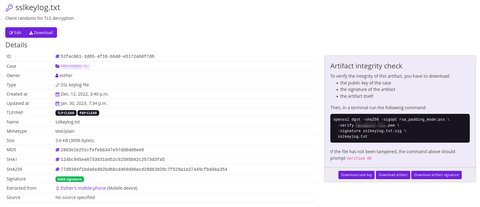
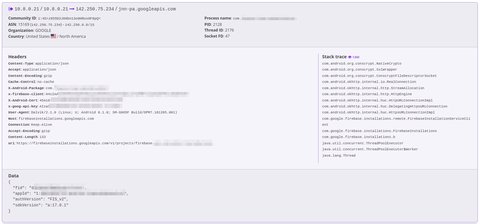
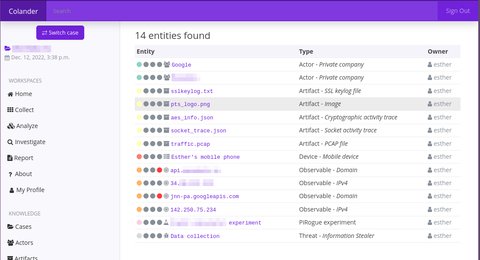
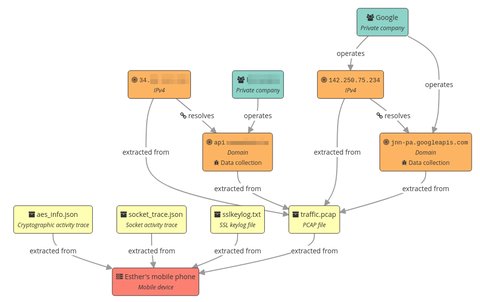
We have manufactured 5 more PiRogues. They will be shipped next month. ColanderWe have finished the basic implementation of the case management and quick search. Since Colander handles artifacts/evidences, we have implemented the automatic signature of all of them with an RSA key that belongs to the case (each case has its own signing key). A user can then easily verify the origin and the integrity of a given artifact/evidence. We have improved the traffic decryption UI. Finally, we have implemented a really basic graph representation of a case. This graph represents the semantic link between the different entities that belong to a given case.
Communication & OutreachWe have slightly improved the website landing page by adding the list of the main capabilities of PiRogue and a 3D view of a PiRogue. We have also added privacy-preserving analytics on the project’s website based on Plausible.io. 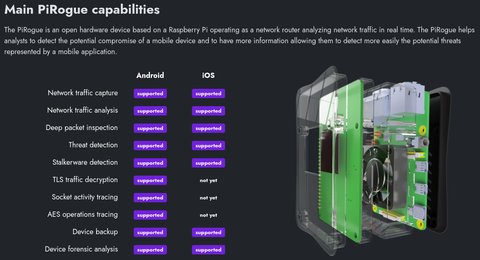 What we plan to do next month
ChallengesRaspberry Pi 4 model B shortage has a negative impact on project adoption. Even if it is possible to turn an old PC or laptop into a PiRogue, it is less convenient than having a tiny device that’s easy to carry. |